Features
There are several ways to protect and obfuscate your .NET code against reverse-engineering. The features at a glance:
Symbols renaming
When we develop a program, we often present the most valuable information in the form of symbol names: names of functions, variables, classes. This information is precious to an intruder who wants to get an understanding of our software.
The simplest and the most effective approach to conceal this information is to make the names irrelevant to what happens inside the program. We will just make the names of all the symbols unreadable — when it is possible.
String encryption and compression
Another thing that discloses information about the functioning of a program is strings. To hide this information, Eazfuscator.NET substitutes the strings in your code with calls of special encryption functions, which render your strings perfectly at runtime, leaving them unreadable to an intruder. Also, these functions make the size of your strings lesser by compressing them.
Your assemblies weigh less!
Code and data virtualization
There are situations when we want to protect a specific part of our program more than anything else. We think of a well-motivated person who would inspect our code and go to desperate measures to extract the intellectual property. In this case, the symbols and strings protection is just not enough.
Here we offer you a radical approach: to change the way your program is presented in memory and on disk. Our code virtualization technology translates your .NET byte code to a randomly generated unrecognizable byte sequence, which still perfectly functions at runtime. In other words, each time you obfuscate your program, we will generate a new custom virtual machine to work for you.
H Homomorphic encryption
Eazfuscator.NET is the world's first commercial obfuscator that started employing the practical elements of homomorphic encryption.
Working in conjunction with code and data virtualization, homomorphic encryption is automatically applied to suitable circuits in your program, making them totally intangible to an attacker.
No one will be able to get through.
Automatic code optimization
Many of us have dreamt of being able to know every performance-sensitive aspect of the platforms and programming languages we use. This way, we would always be careful to write only the fastest code. Still, not many of us are actually aware of all the performance-related details, which often change while the platform evolves.
With Eazfuscator.NET, you don't need to be a .NET performance expert to make the top-performing applications. We perform code optimization for you automatically.
Resource encryption and compression
If your product is ambitious enough, it includes many valuable assets. Almost any popular application includes a designer-created icon set. If you are a game developer, the original game sounds would cost you a lot. When your assembly resources contain security information such as private keys, it becomes very sensitive.
To cover all these things protected, we transparently encrypt the resources for you when you ask it.
Code control flow obfuscation
The .NET languages compilers usually generate similar IL code fragments for the similar fragments of your high-level code. This fact allows the decompiler tools to reverse-engineer the high-level code (in C#, for example) from the .NET assemblies.
Eazfuscator.NET supports an advanced technique called control flow obfuscation which replaces the IL code with functionally equivalent, but slightly different instructions. Decompilers often crash on such code, so this may stop an intruder from trying to break into your assembly.
Assemblies merging and embedding
In some cases, we need to make one assembly from several ones. There are two methods of doing this: merging and embedding.
Eazfuscator.NET merges or embeds assemblies for you in an easy way: you need to add one line of code to your project, where you specify which assembly to mix in. We are responsible for all this to be done correctly and quietly — during the obfuscation process.
XML documentation filter
If you are developing a class library, it is very probable that you use the auto-generated XML documentation files. The security problem concerning them is that they contain information describing your library implementation details: names and descriptions for private types, methods, and fields.
We take care to automatically remove all the implementation-disclosing data from the XML documentation files.
Debugging support
After your assembly is obfuscated with Eazfuscator.NET, it doesn't become a brick of non-debuggable mess. You can always get a line number where an unhandled exception appeared, view a readable stack trace, and even attach the debugger to walk through your obfuscated code.
Supported platforms and technologies
-
 .NET 5.0 – 10.0
.NET 5.0 – 10.0
- .NET Standard versions 1.0 – 2.1
- .NET Core versions 1.0 – 3.1
-
 .NET Framework versions 2.0 – 4.8.1
.NET Framework versions 2.0 – 4.8.1
- XAML with intelligent renaming of symbols for WPF, MAUI and UWP
- Enterprise-grade technologies: ClickOnce, VSTO, and many others
- Universal Windows Platform (UWP)
- Gaming technologies: Unity, MonoGame, XNA
- Third-party platforms: Mono and Xamarin
-
Integration with
 Microsoft Visual Studio
2005–2022
Microsoft Visual Studio
2005–2022
-
Integration with
 JetBrains Rider
2019.1+
JetBrains Rider
2019.1+
- More…
Compatibility
Assemblies produced by Eazfuscator.NET are rigorously conforming to industrial standards and work wherever .NET can run.

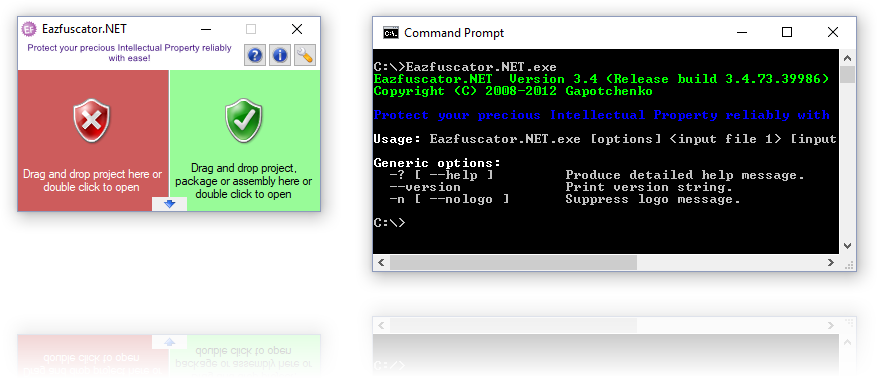
Last but not least. The User Interface
Eazfuscator.NET provides an easy to use GUI as well as a classical command-line interface.